創建存放cloudflare api token的Secret
01-cloudflare-token.yaml
apiVersion: v1 kind: Secret metadata: name: cloudflare-api-token-secret namespace: cert-manager type: Opaque stringData: api-token: $Your_api_token
創建 issuer
02-cloudflare-ClusterIssuer.yaml
apiVersion: cert-manager.io/v1
kind: ClusterIssuer
metadata:
name: letsencrypt-dns01
spec:
acme:
privateKeySecretRef:
name: letsencrypt-dns01
server: https://acme-v02.api.letsencrypt.org/directory
solvers:
- dns01:
cloudflare:
email: [email protected] # 替換成你的 cloudflare 郵箱賬號,API Token 方式認證非必需,API Keys 認證是必需
apiTokenSecretRef:
key: api-token
name: cloudflare-api-token-secret # 引用儲存 cloudflare 認證資訊的 Secret
自簽Certificate
03-cloudflare-Certificate.yaml
apiVersion: cert-manager.io/v1
kind: Certificate
metadata:
name: cert-yourdomain-com
namespace: default
spec:
dnsNames:
- cert.yourdomain.com # 要簽發證書的域名
issuerRef:
kind: ClusterIssuer
name: letsencrypt-dns01 # 引用 ClusterIssuer,指示採用 dns01 方式進行校驗
secretName: cert-yourdomain-com # 最終簽發出來的證書會儲存在這個 Secret 裡面
創建ingress
04-cloudflare-ingress.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: tls-test-ingress
annotations:
# add an annotation indicating the issuer to use.
cert-manager.io/cluster-issuer: letsencrypt-dns01
spec:
ingressClassName: cilium
rules:
- host: cert.yourdomain.com
http:
paths:
- path: /
pathType: Prefix
backend:
service:
name: nginx-service
port:
number: 80
tls:
- hosts:
- cert.yourdomain.com
secretName: cert-yourdomain-com
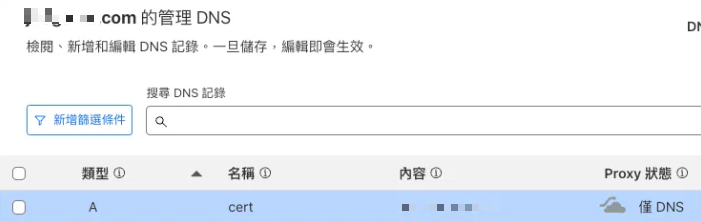
Cloudflare創建一筆要產生TLS的DNS
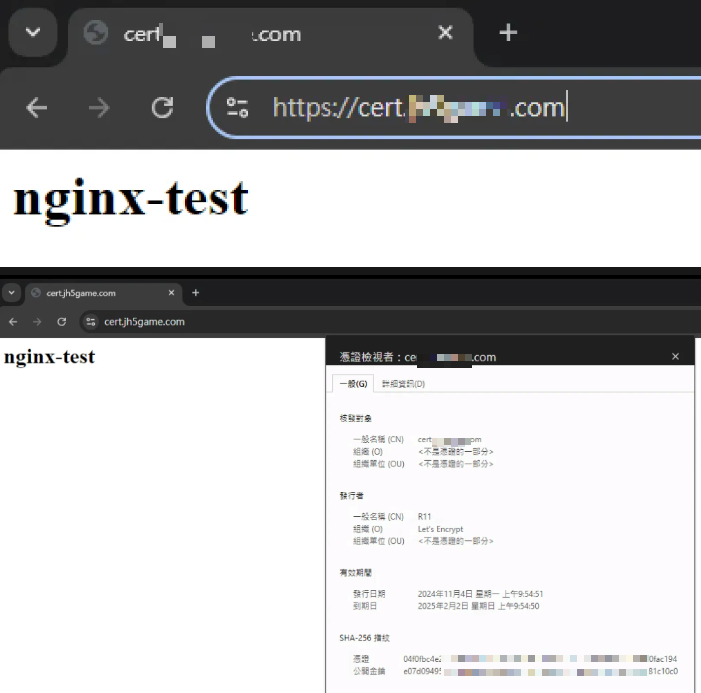
訪問url 檢查tls是否正常